The Nog is made! It’s aging in my refrigerator right now. It’s Thursday, and I’m back in the chair with Mark Starling, Seth, John, and the First News 570 crew. This week’s top tech stories: ape NFT sells for a fraction of the price, small software component leads to big headache, and Apple releases an Android app to stop stalkers. You can listen to Mark and I point and laugh while talking about the wild and crazy technology world every Thursday morning, LIVE at 6:43am Eastern by tuning into WWNC on the iHeartRadio app.
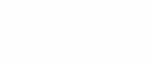
APE NFT SELLS FOR FRACTION OF THE PRICE
Max, who goes by maxnaut online, mistakenly sold one of his NFT art paintings for a tenth of its value on the Ethereum blockchain. The NFT in question was one of the works in The Bored Ape Yacht Club collection of virtual (digital?) artwork. Max listed his work for 0.75 eth, or Ether, the cryptocurrency on the Ethereurm blockchain. He meant to list the art for 75 eth, instead. As soon as he clicked the button; a bot, or automated program paid a heft amount in gas fees (8 eth or $4,029) to scoop up the artwork for $2,844, and then later sold it for $284, 495. Here’s why this really sucks. Some high money holder of Ethereum paid two times the value of the transaction (the cost of the artwork $2,844) to get ahead of anyone else on the blockchain and make the sale. Most regular people wouldn’t pay transaction fees higher than the value of the item. (Unless it’s Ticketmaster) I’m still not sure where I land on cryptocurrencies and NFTs, but they ARE NOT solving problems. They are inventing new ones and exacerbating inequality issues that are already out of balance in the world. I’m off my soapbox.
CLOUD AND SOFTWARE WORLD ROCKED BY SMALL PIECE OF SOFTWARE
The big news. The cloud computing and web software world was rocked to its foundation this past Monday. A small component used for writing event logs, or messages used for debugging, had a vulnerability that caused companies to scramble. The event logging component log4j is used in millions of software applications and devices around the world. Hackers figured out a way to exploit log4j to remotely execute programs on another server. We even went scrambling for a minute checking which services used log4j and where they were. The exploit possibly caused an outage on AWS which also affected Zoom users yesterday. If you’re an end user there’s nothing you can really do. Makers of your software will need to patch their systems. Two patches were released to fix the issue because…the developers didn’t completely fix the issue. Microsoft is reporting that state actors are trying to exploit the vulnerability to gain access to systems. There’s been a few high profile ransom attacks already reported. How big is this exploit? Over half of corporate networks, 100 million devices, and the US government is making agencies patch their systems by Christmas Eve.
GASP: APPLE RELEASES ANDROID APP TO PREVENT AIRTAG STALKING
Apple AirTags are little tracking devices that can be placed on items, in the car, or around the house to help people find things. The devices work because Apple device form a sort of mesh that creates a large area network used for tracking. Like many technologies, the technology was used for nefarious purposes by stalkers. Stalkers were using the tech to track women by dropping them in women’s coats or purses or affixing them to women’s cars. Apple made an update to their AirTag technology to alert users when an unknown AirTag is near their person. Apple…has releases an Android app that does the same thing.